#66 AI is trendy, crypto is not
AI has taken the spotlight as the most pressing technological breakthrough, while crypto struggles to survive in the regulatory adversarial environment.
We are delighted to announce our first partner for Carbono Insights. This issue is sponsored by Audita, an auditor firm for Web 3 protocols and dApps. Audita performs high-quality security reviews of EVM-based web3 projects. It helps projects stay ahead of hackers.
If you’re building or working on a Web 3 project, contact them to learn how they can help you make your protocol more secure.
Learn more about Audita through their website, Twitter and Medium.
Things look so sluggish in crypto lately! Regulatory uncertainty and the confusing macro environment have everybody in cautious mode. As a result, prices move slowly, and there’s no controversy to feed headlines. Some might take this as a sign of stagnation, but working in silence is a blessing.
AI has taken the spotlight from blockchain technology, but the new and the old buzzword can cooperate in some areas.
Bitcoin is bustling. Ordinals have boosted the space.
Who is suspicious of who now? Some data and news show how the crypto world is the one that’s severing connections with the traditional world.
Tokenomics is the art of designing and managing crypto assets. We briefly explain what token unlock is in the context of tokenomics and why it matters these days.
The countdown is on to the implementation of the European regulatory framework.
We explain what a smart contract audit is and how the lack of audits is behind many of the most outstanding hacks in crypto.
We asked Dall-E for a portrait of the Uncanny Valley, and this is what it came up with. We wanted to illustrate the progress of AI, which, these days, is also news in the crypto sphere.
1. AI | Where do AI and blockchain meet
NVIDIA sounds similar to the Spanish word for jealousy (”envidia”), which many crypto people are feeling lately towards AI. After presenting its latest earning report, NVIDIA’s stock skyrocketed the company into the Wall Street Olympus.
At today’s prices, Nvidia’s market capitalization is $963.18 billion, officially outpacing Berkshire Hathaway ($700.59 billion), Meta ($671.53 billion), and Tesla ($612.25 billion). Decrypt
The promised financial revolution by blockchain now sounds like an old tale compared to the constant stream of boasts from AI. Even Paradigm, one of the leading crypto VCs, is rebranding, removing their focus on crypto from their website homepage, and opening up to “research-driven technology.”
There are a few areas of promising cooperation between AI and blockchain technology: authentication of contents, incentivized computer processing, incentivized human contribution to AI training, and transaction automation.
These are areas of promising cooperation.
2. Bitcoin | The curious case of Bitcoin evolution
There’s been a handful of unexpected developments in the Bitcoin ecosystem recently. First, there was all the buzz around Stably, dubbed the first USD-pegged stablecoin on the Bitcoin blockchain—the launch of BRC-721e, a protocol to transfer Ethereum NFTs to Bitcoin Ordinals. Even long-time bitcoin enemy and gold maxi Peter Schiff has embraced the Ordinals and has launched a collection of inscriptions. The collection still looks like a jab at crypto, but it’s on-chain!
In these times of monotony, seeing Bitcoin as the busiest corner of crypto feels strange. It all started with Ordinals, the protocol that used the changes in the Bitcoin protocol introduced by the last upgrade, Taproot, to create an equivalent to NFTs on the primordial blockchain. Ordinals attracted liquidity and talent, and there are currently a lot of innovations happening around Bitcoin. At the end of the day, while there’s some fragmentation in crypto between fans of different L1s or L2s, everyone who’s ever entered the space likely holds some BTC.
The way Bitcoin is evolving these days is unique. First came the network effects (for starters, everybody holds the native currency), then the alternative use cases emerged (NFT collections started sprawling). Now we need all the infrastructure: improved wallets, marketplaces, and scalability solutions.
3. TradFi | Crypto retreats from the real world
Two unrelated news from last week tell a similar story.
Before the debt ceiling agreement was reached last week, Circle, the issuer conglomerate of USDC, eliminated all U.S. Treasury bonds from its stablecoin’s backing reserves.
In the meantime, the amount of ETH and BTC balances in centralized exchanges hit a five-year low. This is because most of the supply of these two cryptocurrencies is now held and traded in decentralized “facilities.”
These two pieces of information show how, at a time when US regulators have doubled down their efforts against crypto, crypto also is showing signs of mistrust towards traditional financial and political institutions. As a result, Ethereum and bitcoin holders and stablecoin issuers do not feel comfortable leaving their capital at the expense of politicians and regulators.
Who mistrusts who?
4. Tokenomics | Token unlocks explained
When a project designs the launch of a token through an ICO, SAFT agreement, or airdrop, for example, there’s a defined initial allocation to different stakeholders, such as early users, investors, or team members. This distribution is designed to help onboard and incentivize a diverse community and align their interests. Tokens are expected to embody, in this context, a common goal: all holders are expected to pursue adding value to it. And to ensure this, vesting conditions usually apply to prevent initial holders from selling early.
Token unlocks provide insights into a crypto project's long-term commitment and stakeholder behavior. When tokens unlock, stakeholders rapidly selling can indicate a lack of confidence or dissatisfaction, conveying a powerful message about the project's viability. Analyzing token unlock schedules helps assess project sustainability and stakeholder sentiments. Top projects like dYdX, GMX, and Blur are examples of top projects approaching token unlock dates.
https://token.unlocks.app/
5. Regulation | Countdown to MiCA begins
The countdown for the implementation of MiCA has started. If this were a movie, the director would show us a closeup of a stupidly large digital clock with a stupidly loud beep signaling the beginning of the timer. But this is not a movie; it’s EU politics. So the timer would show a countdown for 12 to 18 months, which is everything but thrilling.
Nevertheless, there are reasons to be excited. MiCA reinforces Hong Kong's message last week: there’s life outside of the US. The lack of regulatory clarity is why crypto has become so dull lately, but the EU and HK are living proof that regulation is possible.
6. Security | What are smart contract audits, and what they matter
A smart contract is a self-executing piece of software with the terms of an agreement written into code and executes specific actions based on predefined conditions. Examples of smart contracts are lending protocols, where the requirements of a loan (amounts, interest rates, liquidation conditions, etc.) are enforced by code.
Smart contracts are generally immutable and irreversible once deployed on a blockchain, and they are critical in the operations of blockchain infrastructure (blockchains, rollups,…) and decentralized finance protocols (decentralized exchanges, staking protocols, lending platforms). The funds locked inside of smart contracts often constitute succulent bounties for hackers.
Smart contract auditing is the process of evaluating and analyzing the code and functionality of a smart contract to identify potential security risks. Audits are performed by specialized third parties who search for vulnerabilities that malicious actors could exploit. It has happened in the past, and it will continue to happen.
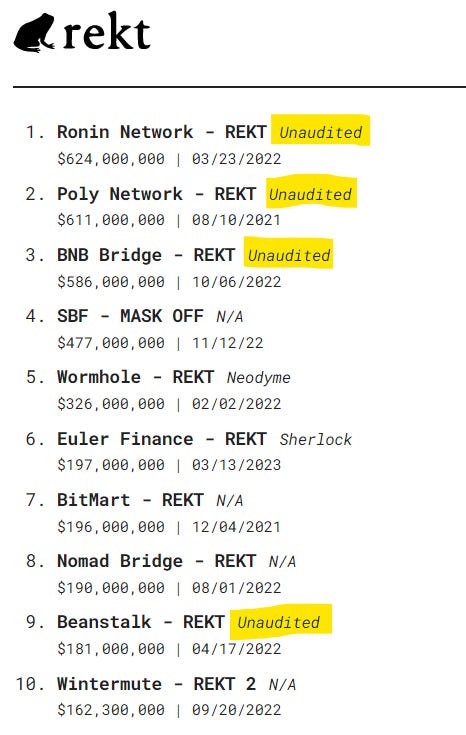
A quick look at the Top 10 most prominent hacks can give you a sense of the size of the problem. Hacks are becoming more innovative and sophisticated, while only some protocols learn from past mistakes. Every week there are reports of numerous price oracle manipulations, front-running attacks, and fallback function exploitations that prove even the oldest hacks in the book still cause headaches today.